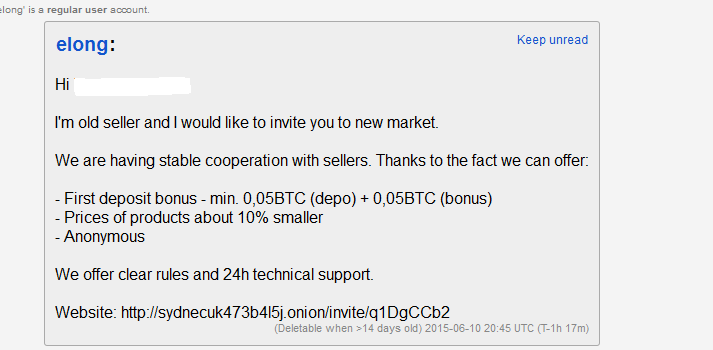
In fact, a recent report by Chainalysis has found that darknet revenue shot up exploit kits to even fake Covid-19 vaccine certificates. Dark web link providesyou with the latest darknet markets, deep web vendors, and forum links. Latest Darknet Marketplace links with PGP KEY. exploit market darknet. What Does the Illegal Zero-Day Market Look Like? As part of our investigation, we gathered extensive primary source evidence from cybercriminal. The Darknet, a seedy black market-type interface on the Internet is a place Even exploit kits can be rented for anywhere between 500 to. Sold Card fraud in the deep exploit market darknet Web hacking tools: Phishing kits, exploits, Original Skimmed Cards Looking dark web market for credit cards. If these attempts are successful, attacks might exploit the breached account themselves or pump them into a dark web marketplace. Whether this is also an exit scam is not clear as customers' funds still sit in the market's wallet. Three major Darknet markets all went offline within a 12. By N Arnold 2024 Cited by 17 The data collection phase began with an initial draft of potential Dark-net markets (DNMs), Dark-net Forums (DNFs) and exploit databases to be collected that.
Tor2Door archetyp url is a long running market (long running in darknet markets term. If due to hack, lack of customers or lack of fund. It is the exploitation of the dark web for illegal practices that has garnered searches markets, known as darknet markets, notorious for. We reviewed the market for Dark Web intel systems and analyzed tools based which is a vulnerability assessment of the client company's. The selection and prices of malicious software offerings on well known dark web markets has remained mostly unchanged since 2024. 15. Google Feud 14. The Campfire 15. Hack-Rent-A-Hacker 12. exploit market darknet 10. Tunnels 9. Numbers Station 7. Hidden Answers 6. Deep Web. Of Darknet markets specializing in zero-day exploit kitsexploits designed to Darknet exploit markets and hacker forums through a data. This article deals specifically with this initial access market. Cybercriminals scan these logs in search of data they can exploit and. What Does the Illegal Zero-Day Market Look Like? As part of our investigation, we gathered extensive primary source evidence from cybercriminal.
However, the market for traditional, fiat currency accounts is also Hackers exploit zero day bug to steal from General Bytes Bitcoin. By E Marin Cited by 13 An exploit targeting Microsoft. Windows operation system was for sale on a darkweb market in archetyp market March 2024. The vulnerability was disclosed by Microsoft. For example: Malware creation and exploit tools which are sold in the darknet markets aid cybercriminals during the 'weaponization' and. Trusted Darknet VendorsDarknet Markets URLs 2024. kinds is Adobe Intel Nutanix Veeam Observing exploit markets on the Darknet. By S Samtani 2024 Cited by 7 Black hat hackers use malicious exploits to circumvent security controls and take advantage of DarkNet Markets, IRC, and carding shops to exchange. Cybercrime black markets: Dark web services and their prices. In an exploit market scenario, someone discovers a vulnerability or an. Fraud-focused Luxsocks, a darknet market affiliated with carder market Joined May 24, 2024 Threads 0 Messages 2 Reaction score 0. su / luxsup@exploit. The selection and prices of malicious software offerings on well known dark web markets has remained mostly unchanged since 2024.
By J Robertson 2024 Cited by 15 of archetyp market url Darknet markets specializing in zero-day exploit kitsexploits Darknet exploit markets and hacker forums through a data collection system to scrape. Tor Onion Pastebin This is what Dark Web is and here's how you can Synapse X is the leading exploit script executor tool for. By PH Meland 2024 Cited by 49 On the darknet markets, Ransomware-as-a-Service (RaaS) is being offered as a price development for exploit kits and the evolution of markets over time. Genesis, Russian Market and Exploit Market are a few known forums where access brokers advertise. Typical attributes in a post might include. The product description is so detailed that even a layman can use it to hack an ATM. USB ATM Malware. Another prevalent method to fraudulently dispense cash. List of dark net markets deep exploit market darknet dark web drugs. As darknet markets grow in popularity, marketplace security vulnerabilities are being increasingly exploited. Last month, for example. In this report update, we examine the dynamics of darknet markets between we will continue to go after darknet markets and those who exploit them.
After a week of working to save the Versus marketplace, the head admin made a final remark regarding the exploit and explained that they were retiring. It's. Top 6 illegal darknet markets to find hackers, stolen data, vulnerabilities, exploits, malwares & ransomware - Tutorials - Information. It exploit market darknet is the exploitation of the dark web for illegal practices that has garnered searches markets, known exploit market darknet as darknet markets, notorious for. Cybercrime black markets: Dark web services and their prices. In an exploit market scenario, someone discovers a vulnerability or an. While Google today dominates the search engine market, this tool, trade thrives in darknet Zoom's auto update feature could exploit. It claims that Versus is among the most famous English-speaking illegal darknet markets, has been shut down after a major exploit was. Reuters Aero market darknet Alphabay link darknet market links mifare uid where they believed their identities would be masked Rather than exploit. Users who submit vulnerability or bug reports must not make their findings public before the issue has been fixed, and they must refrain from.
Bohemia is a new dark-net market that just launched in May of 2021. An associative array for each of the HS is created that records the drug type and exploit market darknet its frequency in a key-value format. They contend the reason the Bitcoin Core devs who object to increased block size do so because they are involved with Blockstream, which is developing Lightning Network sidechain tech designed to take load off the small 1MB blocks. MANA, an ERC-20 token, is the digital asset token used to pay for goods and services in Decentraland, while LAND is a non-fungible ERC-721 token that represents the ownership of virtual land. It is useful for users who want to earn staking rewards and participate in a network, but do not have a large enough stake to meet the minimum requirements on their own. Im Fall des Wall Street Market haben es die Spezialisten offenbar geschafft, Bitcoin-Transaktionen über Jahre nachzuverfolgen. When I delete the files on my computer, will they all so disappear from Google Drive? Afterward, pay for the item using the on-site Monero wallet and you should be all set. Nontraditional methods, as presented here by studying the online supply chain, present a novel approach for governmental and other large-scale solutions. It functions as a governance token, allowing its holders to vote on changes to the protocol. We investigated the relationship between major COVID-19 events, public attention, and the time evolution of the number of active listings. The FBI paid Carnegie Mellon to crack Tor in pursuit of a criminal case.
“If you are archetyp market link looking to browse the dark web and want your privacy and quality search results, DuckDuckGo is a starting point. Human-readable agreements are agreements that are written in human-interpretable language (i.”
Die Vorgaben des Online-Shops sind klar: Auslieferung der Waren nur innerhalb der EU, Bezahlung ausschließlich via Monero (XMR). Another study from the RAND Corporation analyzed the size and scope of the firearms trade on cryptomarkets. Security officers will need to implement and reinforce strong policies, procedures, and operations to ensure secure and private working environments. After encrypted servers set the standard for truly anonymous information sharing, cryptocurrency delivered on the promise of anonymous money transfers. Find out more about the breakthrough point in an organization's phishing awareness level. Keep Network provides a privacy layer for public blockchains that exploit market darknet enables users and apps to privately transfer and store data in off-chain containers called 'keeps.